Affecting thousands of websites and forcing them to promote unlicensed Chinese gambling websites, a malicious JavaScript hijack injection has spread across the internet. Experts estimate that JavaScript injections have compromised roughly 150,000 legitimate websites.
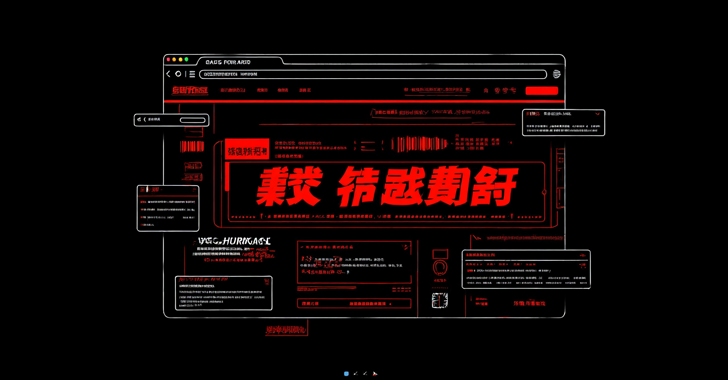
Redirecting them to pages promoting gambling, the hackers behind this promotion of illegal Chinese gaming platforms have leveraged inframe injection to display a full-screen overlay on the infected websites. Instead of finding the site they are looking for, customers encounter an interface promoting a Chinese gambling website.
According to experts, the overlays sometimes vary from site to site. The hackers pose as legitimate betting websites in some cases, like bet365, which previously announced that it will stop its business in China. Usually, similar cases employ official gambling company logos and branding to convince users that the offer is legitimate.
Himanshu Anand, C/side expert analyzed the threat. He says that the mechanism is the same in spite of the slight differences between infected websites. He also said that as of the time of his writing, hackers had infected over 150,000 websites.
C/side is the only autonomous detection tool for assessing 3rd party scripts. It specializes in shielding websites from similar fraud. Experts of C/side first caught wind of the Chinese gambling JavaScript injection fraud in February.
Anand says that the attack highlights the fearsome adaptability of threat actors, who keep on evolving and scamming people. He added that these attacks are increasing as more websites become affected daily.
Himanshu Anand says that if you suspect your site might be impacted, review all scripts for hidden HTML entity encoding or suspicious <iframe> injections. As always, ongoing vigilance and regular site auditing remain your best defenses against attacks like these.
Anand provided more insights into the mechanisms of the scam in the official release of the c/side.


